Data Anonymization Tool
Operationalize GDPR compliance with a solution built for the modern regulatory landscape. The DeliveredSoft Anonymization Tool is specifically designed to help organizations fulfill the “Right to be Forgotten” (Article 17) without compromising business continuity. While GDPR mandates the erasure of personal data when it is no longer necessary, businesses must often retain transactional and financial records for legal and audit reasons. Our tool solves this conflict by replacing personally identifiable information (PII) with anonymized values. This ensures individuals can no longer be identified while the integrity, structure, and usability of your historical business data remain perfectly intact.
Key benefits
- GDPR article 17 compliance: Seamlessly handle "Right to Erasure" requests by anonymizing customer and worker data on demand.
- Secure non-production environments: Safely share demo, test, or audit environments with external partners without exposing real PII (Personally Identifiable Information).
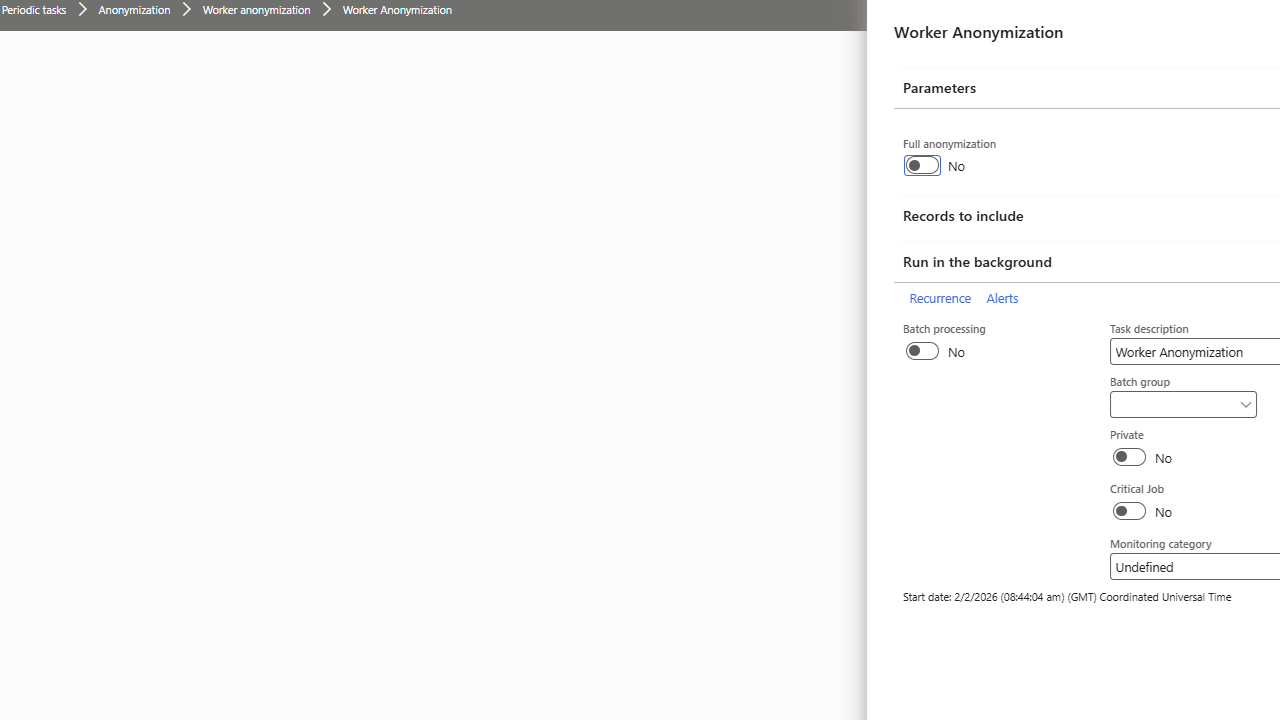
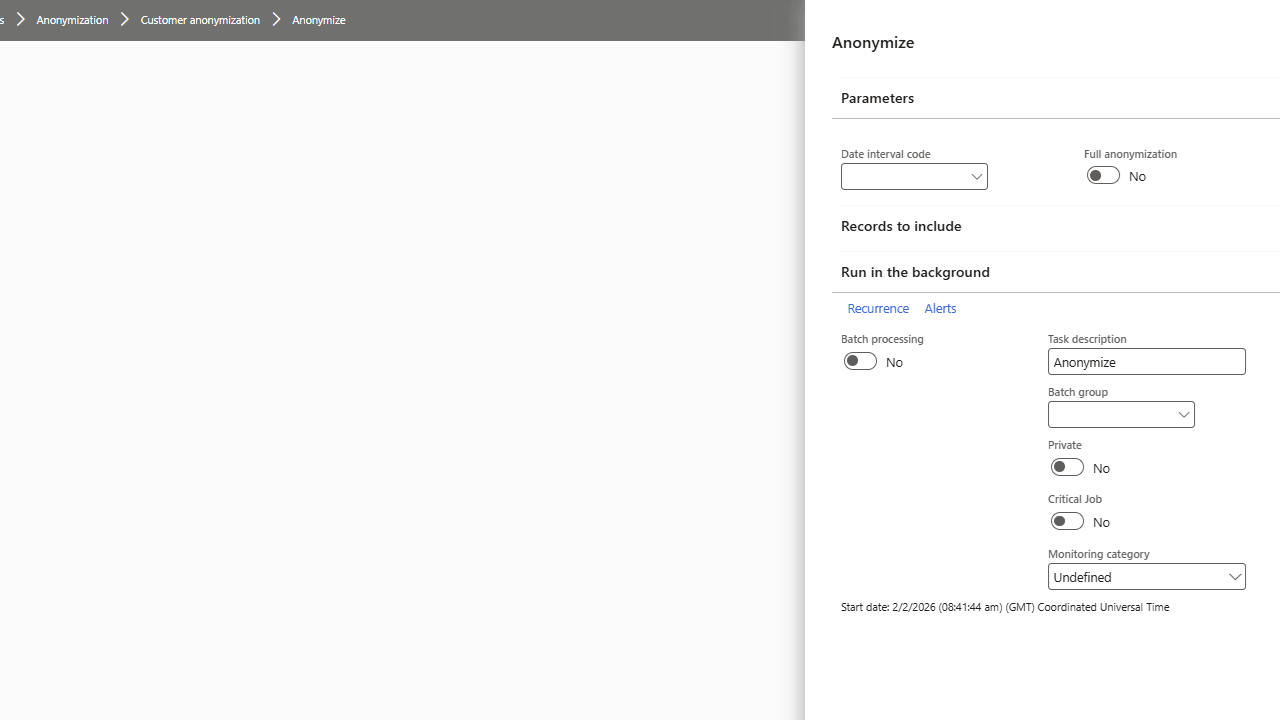
- Automated and on-demand: Run scheduled mass anonymization jobs or mask individual records directly from the customer or worker page.
- Preserve data integrity: Anonymize data while keeping the format and referential integrity intact, ensuring your business logic still works perfectly.
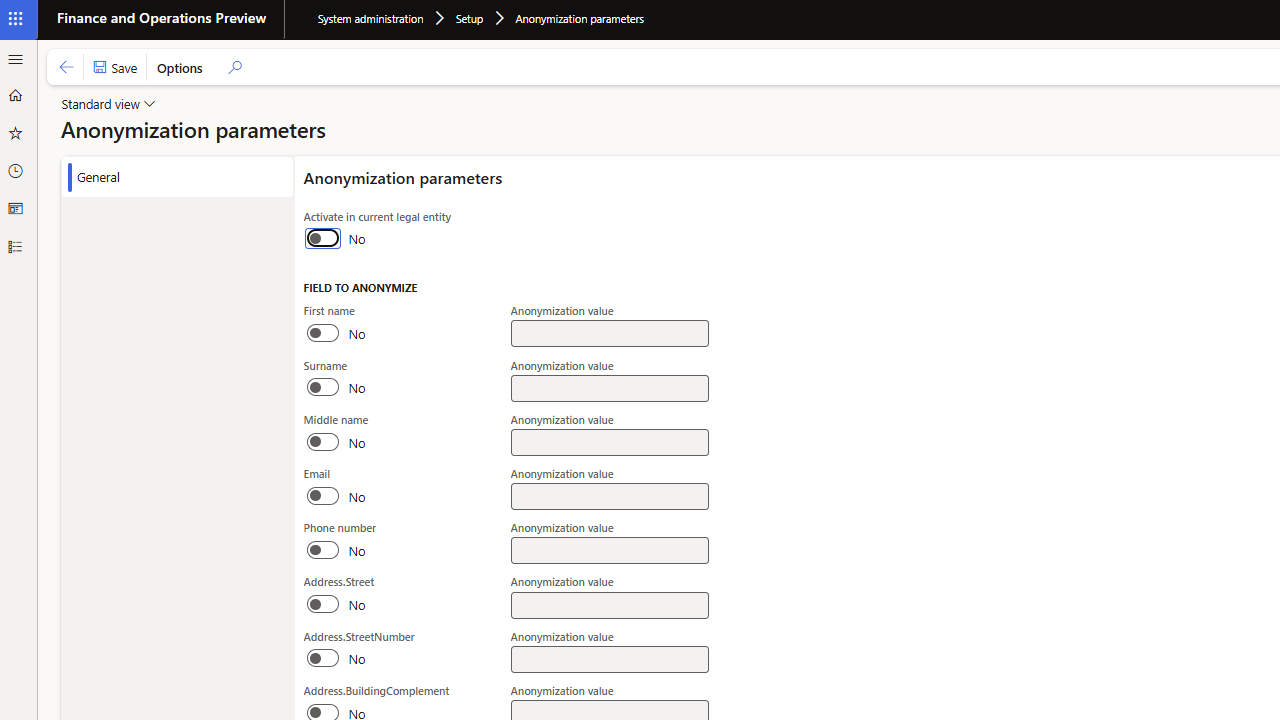
- Flexible configuration: Define exactly which tables and fields should be anonymized using a simple, code-free interface.
Examples of usage
When a customer exercises their "Right to be Forgotten," a user can trigger an on-demand anonymization of that specific record. The name, phone, and email are scrubbed, but the sales history remains for VAT reporting.
After refreshing a UAT or Dev environment with fresh production data, run a mass job to anonymize all customers, vendors, and employees, ensuring no real PII is exposed to developers or testers.
Set a recurring rule to automatically anonymize employee records for anyone who has been inactive for more than 10 years, adhering to labor law data retention limits without manually searching records.
Provide auditors or consultants with a copy of your database where sensitive identity data is masked, allowing them to verify financial accuracy without ever seeing the actual names of your clients or staff.
How it works?
Select system or custom tables and fields that contain sensitive data. You can build search and filtering rules to narrow down the exact scope of what needs protection.
Decide how to replace data. Use hashing, scrambling, or fixed-value replacement to ensure the data format remains valid (e.g., maintaining a valid-looking email structure) while the content is rendered anonymous.
Trigger anonymization for a single record from the entity page, or schedule high-performance batch jobs for mass database cleaning in non-production environments.
Every request and execution is logged. The system provides comprehensive reporting on anonymization status, allowing your DPO (Data Protection Officer) to track compliance and accountability.
Everything starts with a conversation